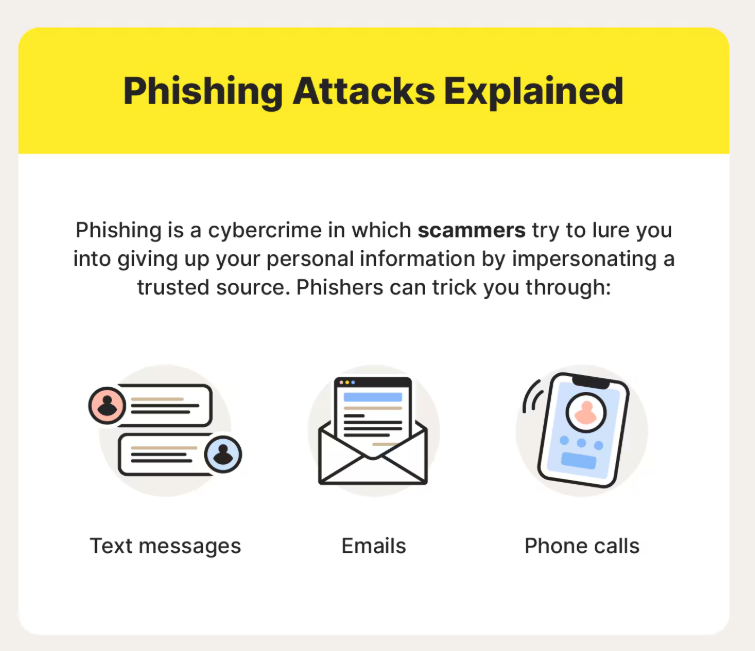
Phishing is a type of social-engineering attack where criminals pretend to be a trusted person or organization to trick you into revealing sensitive information (passwords, bank details, or company data) or into performing an action (clicking a malicious link, downloading malware, or making a payment). It most commonly arrives as an email but also appears via SMS (smishing), voice calls (vishing), instant messages and social media. Attackers use urgency, fake branding, spoofed sender addresses and personalized details to make the request look legitimate.