Welcome to your first lesson for Cyber Security Awareness Training!
The core competency of this module:
The Understanding that the role of passwords can play in cybersecurity. Passwords are you first line of defense – it is important to understand how we can construct and utilize passwords to keep a strong security posture.
At the end of this module you should be able to:
- Understand why passwords matter
- Be able to develop strong passwords
- The dangers of password re-using
- Password managers
- Two factor authentication
So why do passwords matter?
Passwords are the first and often only barrier between attackers and your accounts, systems, and sensitive data.
A single compromised credential can give an attacker access to email, financial systems, HR records and admin tools – and from there they can steal data, commit fraud, impersonate staff, or cause costly business disruption.
Because attackers automate and scale attacks, even small, everyday password mistakes (reuse, short words, predictable patterns) quickly become high-impact security failures.
Did you know?
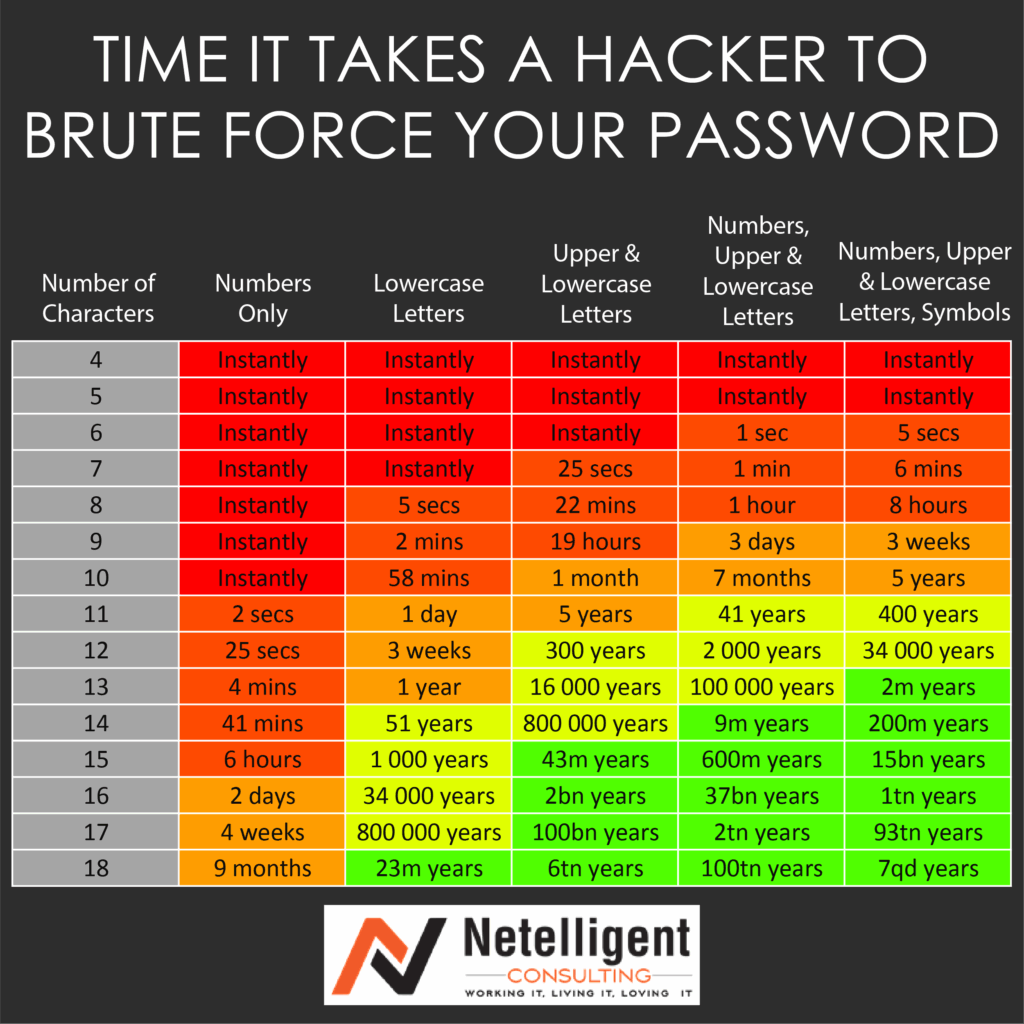
Weak passwords can be cracked within seconds! Take a look at the chart below to see how your strong current passwords are.
Closing thoughts on password importance:
Strong, unique passwords reduce the chances that automated tools or simple guessing will grant attackers entry.
When combined with good practice tools (which we will be learning about in upcoming modules) such as password managers and MFA. We will greatly reduce the risk of attacks.